On 20 May, Paradigm researcher, samczsun reported an attack on the Tornado Cash mixer’s decentralized voting protocol. A hacker managed to secure an absolute majority of the voting power, and as a result, governance of Tornado Cash was monopolized by an unknown wallet address.
The method used for the attack is both elegant and worrying at the same time. The hacker copied a previous routine proposal that was passed, mentioning that it used the "same logic of proposal #16" in the description, but added a backdoor function that allowed the logic of the contract to be completely changed.
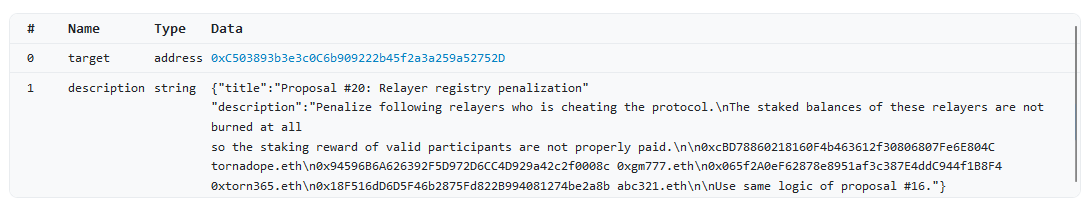
Somewhat predictably, no one took the time to check the contract before signing, and the proposal was approved, granting full control to the hijacker and again highlighting a weak point of the decentralized governance concept.
The attacker pocketed 1.2 million votes, almost twice as many as required to approve any proposal, including the withdrawal of voting stakes or even a complete shutdown of the service.
Next, the hacker drained voting contracts, pocketing a total of 483,000 of Tornado's TORN governance tokens. Ironically, about 380,000 of these tokens were then swapped to ETH and laundered through Tornado Cash itself.
The next day the hacker published a new proposal that returned control of Tornado Cash to its DAO and unanimously approved it.
As another Tornado observer put it: "Either they're giga trolling or it will end up being an expensive but not disastrous lesson in Governance security"
TORN price reacted to the incident by dropping from $6 to $3.8. After control was returned the token price quickly recovered.

We are all sometimes guilty of not reading long license agreements, terms and conditions, and other small-print before clicking the 'accept' button.
In most cases this holds no significant risk. However, in decentralized systems of governance it could turn out to be a very expensive mistake.